How to Create a Safer Bluetooth Connection
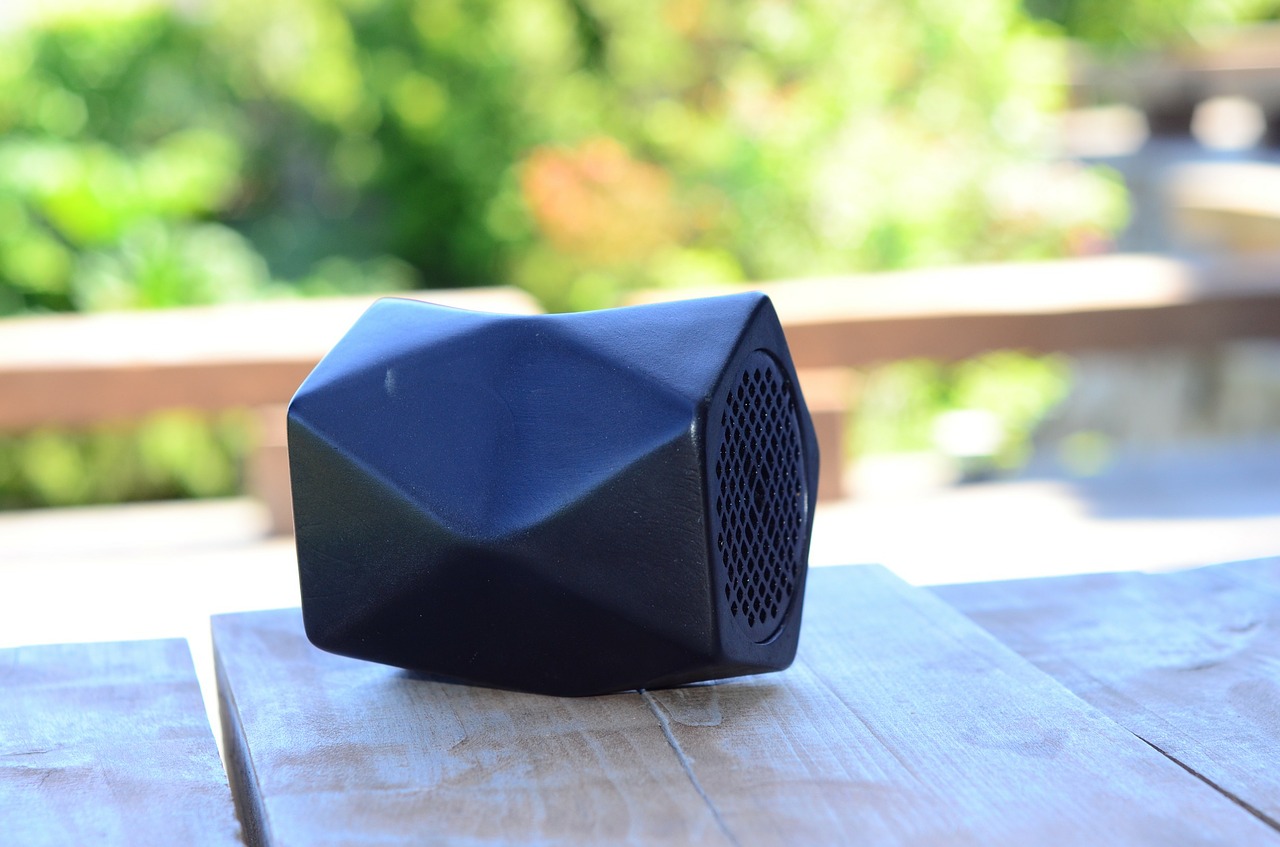 Bluetooth technology is commonly used for mobile phones and various other wireless IoT solutions. The implementation of the BLE standard is what makes Bluetooth suitable for IoT sensors that are powered by batteries for wireless IoT solutions. Named after a Viking ruler, Bluetooth was discovered at Ericsson back in the year 1994 by Dr. Haartsen. It works in the frequency range between 2.400GHz and 2.4835 GHz. Despite occupying frequencies similar to Wi-Fi, it can only be used for short ranges and consumes less power. For optimal use of this technology, it is imperative to understand how to prevent unauthorized access to bluetooth speakers. Some tips to help you create safe Bluetooth connections are highlighted below.
Bluetooth technology is commonly used for mobile phones and various other wireless IoT solutions. The implementation of the BLE standard is what makes Bluetooth suitable for IoT sensors that are powered by batteries for wireless IoT solutions. Named after a Viking ruler, Bluetooth was discovered at Ericsson back in the year 1994 by Dr. Haartsen. It works in the frequency range between 2.400GHz and 2.4835 GHz. Despite occupying frequencies similar to Wi-Fi, it can only be used for short ranges and consumes less power. For optimal use of this technology, it is imperative to understand how to prevent unauthorized access to bluetooth speakers. Some tips to help you create safe Bluetooth connections are highlighted below.
Ensure the Bluetooth Version on Your Device Is Updated
There are many different versions of Bluetooth available on commercial devices, all of which are compatible with the earlier versions. The pairing and security mechanisms for the previous versions are a bit different from those of the newer versions. When connecting to an older version of Bluetooth, the security mechanism used will be that of the older version. The main factors that you should consider regarding security are pairing algorithm and encryption algorithm. When acquiring devices with Bluetooth capabilities, ensure that you consider both.
Whenever Possible, Avoid Using Only Work Pairing
Devices that use Bluetooth version 2.1 and above implement the Secure Simple Pairing mechanism. That mechanism helps to make the pin pairing process much simpler and more flexible. The four association models are Number Comparison, Just Works, Passkey Entry, and Out Of Band. A majority of devices use the Just Works association even though there are other options. Just work can allow attacks such as man-in-the-middle as it passes some values in plain text between the devices. Consider using other associations that are more secure.
Always Use the BLE Link-Layer Encryption
 BLE devices implement the AES-128 protocol. The protocol encrypts all data within the payload to ensure that it remains confidential. A message Integrity Check is also included in the packets, which is used to validate message integrity and prevent replay attacks. The host is responsible for initiating the encryption after making the Bluetooth connection. The slave can only send a security request but cannot start it. Whenever a connection is established, you should always ensure you are using the link-layer encryption.
BLE devices implement the AES-128 protocol. The protocol encrypts all data within the payload to ensure that it remains confidential. A message Integrity Check is also included in the packets, which is used to validate message integrity and prevent replay attacks. The host is responsible for initiating the encryption after making the Bluetooth connection. The slave can only send a security request but cannot start it. Whenever a connection is established, you should always ensure you are using the link-layer encryption.
Use Application-Level Encryption
To enhance the level of communication security between devices, you should consider implementing application-level encryption. With that, the data is encrypted before being transferred via Bluetooth. It can only be decrypted on the other end after the complete file has been received. The only downside to it is that it takes a bit longer to send data, though the duration may vary based on the encryption algorithm used.…



